Can Mesh Networks Make Telegram Unstoppable?
Authors: Science Blog
On March 11, 2026, information security expert Igor Bederov made a bold claim: Telegram could defeat virtually any government blockade by adding mesh network support. Phones would relay messages directly through Bluetooth and Wi-Fi — no providers, no servers, no internet required. The only countermeasure? Jamming radio frequencies. And jamming Bluetooth across an entire city means killing wireless headphones, smartwatches, and car infotainment systems for every resident.
The idea sounds radical. But the underlying technology already exists — and it has already been tested under real political pressure.
Telegram’s Armor — and Its Achilles’ Heel
Telegram is already one of the hardest messengers to block. Its custom MTProto 2.0 protocol uses AES-256 encryption and Diffie-Hellman key exchange. Data is distributed across data centers in Mumbai, Frankfurt, Singapore, and elsewhere. Media files are served through CDN edge caching. Voice and video calls use peer-to-peer connections whenever possible, bypassing servers entirely.
When governments try to block it, Telegram fights back with MTProto proxies — user-deployed servers that create encrypted tunnels optimized specifically for Telegram traffic. These are harder to detect via Deep Packet Inspection than standard VPNs. In Iran and China, community-run proxy networks have kept Telegram alive for years.
But every one of these defenses shares a single assumption: some internet connection exists. When a government cuts the backbone cables — physically, at the ISP level — Telegram goes silent. So does every other app.
In 2024, governments did exactly that 296 times across 54 countries. Access Now documented it as the worst year on record. The economic damage: $7.69 billion. India, Myanmar, Pakistan, and Russia accounted for 71% of all shutdowns. At year’s end, 47 blackouts were still ongoing.
Mesh network — a network topology where every device acts as both a client and a relay. Messages hop from node to node without any central server or access point. If one path breaks, the network routes around it automatically.
Every Phone Becomes a Radio Tower
Picture a crowd passing a sealed envelope hand to hand. The sender wrote the message. The recipient opens it at the other end. Nobody in between can read it. That, stripped to its essence, is a mesh network.
Each smartphone in a mesh performs three jobs: it discovers neighbors via Bluetooth Low Energy (BLE) or Wi-Fi Direct, receives encrypted packets, and forwards them along the chain. Routing happens automatically — protocols decide which path gets a message to its destination fastest.
Three protocols dominate the field, each with a different philosophy.
BATMAN (Better Approach To Mobile Ad-hoc Networking) is proactive. Every node continuously broadcasts OGM packets, scoring link quality through a metric called TQ. It never builds a full map of the network — it simply picks the best next-hop neighbor for each destination. Fast, lightweight, 95% packet delivery in multi-hop tests.
AODV (Ad-hoc On-Demand Distance Vector) is reactive. It sits idle until a message needs sending, then floods the network with RREQ packets. The first reply traces the route back. It conserves battery by avoiding constant chatter but adds startup delay.
OLSR (Optimized Link State Routing) builds a complete network topology using designated MPR relay nodes. Predictable and reliable in dense networks, but overkill for mobile phones with limited charge.
Store-and-forward — a mechanism where a device holds a message in memory until the next node in the chain becomes available. This is the foundation of DTN (Delay Tolerant Networks), designed for environments where connections are intermittent.
Single-hop Bluetooth range: 30 meters indoors, up to 100 in open air. Wi-Fi Direct stretches it to 200 meters but burns battery far faster. In a dense urban crowd, every phone becomes a relay, and the network’s effective radius can reach several kilometers.
Hong Kong, Minsk, Tehran: Field-Tested Under Fire
This technology has already seen action. In September 2019, Hong Kong protesters mass-installed Bridgefy, a Bluetooth mesh messenger. Downloads surged 3,685% in days. People coordinated even in areas where authorities had throttled mobile networks. FireChat, built on Apple’s Multipeer Connectivity framework, had earlier demonstrated that mesh could serve up to 50,000 simultaneous users in a dense protest zone.
In August 2020, Belarus shut down its internet for three days during post-election protests. Organizers recommended Briar — a messenger running on Bluetooth and Tor. It provided end-to-end encrypted communication within a few hundred meters. For longer distances, Tor was needed — which also required internet.
Iran, Myanmar, Kazakhstan — the pattern repeated. Mesh helped with local coordination. It could not replace a full messenger.
The core problem was always scale. Bridgefy worked while protesters stood shoulder to shoulder. Once crowds dispersed, the network collapsed. Worse, researchers from Royal Holloway discovered in 2020 that Bridgefy’s offline mode lacked proper end-to-end encryption and leaked metadata. The company later adopted Signal Protocol, but trust had been damaged.
A Stanford team — Neil Perry, Dan Boneh, and colleagues — proposed a different model in 2022: broadcast every message to every participant, so only the intended recipient can decrypt theirs. This eliminates metadata leakage entirely. An observer cannot tell who is messaging whom. The tradeoff: traffic scales linearly with user count.
Scaling a Bluetooth Chain to 90 Million
Here is where ambition collides with physics. Telegram has over 90 million users in Russia alone. This is not a protest square where a few city blocks need coverage. It is an entire country.
Modern smartphones already carry the necessary hardware. Apple embedded Multipeer Connectivity into iOS back in 2013 — supporting up to 8 devices per session with mesh relay over Bluetooth and Wi-Fi. Google answered with Nearby Connections API: 30+ devices, full mesh topology, automatic self-healing.
From lab demos to a working product for 90 million users, however, is a chasm.
Battery. In mesh mode, a phone continuously scans the airwaves and relays other people’s packets. BLE Mesh uses flood-relay — every node rebroadcasts every message. Under active relay duty, a typical smartphone drains 3–5 times faster than normal. Telegram is an all-day app. If it starts killing batteries, people uninstall it.
Scalability. BLE Mesh experiments show that beyond 100–200 active nodes in radio range, collisions saturate the airwaves. Throughput drops, latency spikes. A Moscow metro car during rush hour holds hundreds of smartphones. If every one relays messages, the channel drowns.
Density gaps. Mesh requires enough nearby nodes to form a chain. Downtown Moscow — no problem. Suburban neighborhoods where houses sit 100+ meters apart — the chain snaps. At night, when people sleep, active nodes drop to near zero.
BLE (Bluetooth Low Energy) — a power-efficient variant of Bluetooth designed for continuous background operation. Range: up to 100 m in open air, realistically 30–50 m in urban settings. Throughput: up to 2 Mbps (Bluetooth 5.0).
The Security Equation
Mesh solves one problem — internet dependency — but opens others.
Sybil attacks. An adversary generates thousands of fake nodes to hijack routing. On Telegram’s centralized network, every account is verified by SMS. In offline mesh mode, that verification is impossible. An alternative trust system is needed — pre-loaded cryptographic certificates, for instance.
Jamming. Bederov identified radio jamming as the only real countermeasure against mesh. Bluetooth operates at 2.4 GHz — the same band as Wi-Fi, microwave ovens, and countless IoT devices. Jamming this band citywide would cripple consumer electronics for everyone. But targeted, localized jammers for specific areas already exist and are already deployed.
Metadata exposure. Even with encrypted message content, the fact that two devices exchanged data is itself information. Bluetooth signals carry device identifiers. Modern phones randomize MAC addresses, but this is not bulletproof. The Stanford broadcast model solves metadata leakage but scales poorly — every message reaches every node.
Legal risk. In several countries, using mesh networks to circumvent government blocks may violate telecommunications law. This is not a technical barrier, but a real one.
What’s Actually Realistic for Telegram
Telegram’s current architecture is cloud-native. Billions of messages flow through servers, sync across data centers, and cache on CDN nodes. Bolting on mesh would mean building a second Telegram inside the first.
The mesh discussion around Telegram intensified in March 2026, but Pavel Durov and his team have not announced integration plans. Expert commentary is based on technical feasibility analysis, not insider information.
The most plausible path is not a full mesh messenger, but an emergency fallback. Telegram detects no internet, then switches to local mesh: text messages via Bluetooth, short voice clips via Wi-Fi Direct. No media files, no cloud sync, no video calls. But the ability to send «I’m safe» or «meet at point B» when everything else is dead.
The SendingNetwork project (arXiv, 2024) points toward a middle ground: a decentralized messaging layer with Proof of Relay (cryptographic confirmation that a node actually forwarded a message) and Proof of Availability (verified uptime via Verkle trees). This tackles the incentive problem — why should an ordinary user spend their battery relaying strangers’ messages?
Meshtastic, an open-source LoRa project, proves that internet-free decentralized communication already works. Range: up to 25 km with an external antenna, record 254 km under ideal conditions. But it handles text and GPS coordinates only — not video messages and stickers.
Most likely, Telegram would move in stages. Step one is already done: MTProto proxies and P2P calls. The next logical step is offline peer-to-peer messaging between contacts within Bluetooth range. Only then would full mesh relay through unknown devices follow. Each step increases autonomy. Each demands new solutions to technical and legal challenges.
The foundation is already in place. Smartphones can find each other over Bluetooth and Wi-Fi. Routing protocols have been battle-tested. Encryption works. The question is not whether this is possible. The question is when someone assembles all the pieces — and whether 90 million phones have enough battery to keep them running.
Frequently Asked Questions
Can mesh fully replace the internet for Telegram?
No. Mesh networks handle text messages within a limited radius — a few kilometers if enough users participate. Syncing chat history, sending photos and videos, running group chats with thousands of members — all of that requires server infrastructure. Mesh is an emergency communication mode, not a replacement for standard Telegram.
Why can’t authorities simply block Bluetooth to stop mesh?
They can — 2.4 GHz jammers exist. But Bluetooth shares its frequency band with Wi-Fi, wireless headphones, smartwatches, car systems, and millions of IoT devices. Jamming it citywide would cripple everyday electronics for every resident. Targeted jamming of specific areas is feasible, but blanket coverage of an entire metropolis is not.
Which mesh messengers work today?
Briar (Android) uses Bluetooth and Tor with end-to-end encryption and no servers. Bridgefy (Android/iOS) works over Bluetooth and was used by Hong Kong protesters, though it had security flaws. Meshtastic operates through external LoRa devices with up to 25 km range but supports only text and GPS. None approach Telegram in features or scale.
How much battery does mesh mode drain?
Significantly under active relay. BLE Mesh requires constant airwave scanning and packet forwarding. In experiments, smartphones acting as active relays drained 3–5 times faster than normal. A realistic implementation would need aggressive limits: infrequent scan cycles, short packet TTL, text-only mode.
Is mesh networking safe from surveillance?
Message content can be strongly encrypted — end-to-end encryption works in mesh just as well as online. The vulnerability is metadata: Bluetooth signals carry device identifiers, and the mere fact of data exchange between two devices can be observed. A Stanford group led by Dan Boneh proposed a broadcast model that hides all metadata, but it scales poorly and dramatically increases network load.
References
Related
- Strong Anonymity for Mesh Messaging (Stanford)
- SendingNetwork: Decentralized Messaging Networks
- Bluetooth Mesh with libp2p: Opportunistic Communications Protocol
- A Formal Analysis of Bluetooth Mesh Provisioning Protocol
- Performance of OLSR and BATMAN in Multi-hop Mesh Ad Hoc Networks
- Enhancing Reliability and Stability of BLE Mesh Networks: M-O-AODV
Related Articles
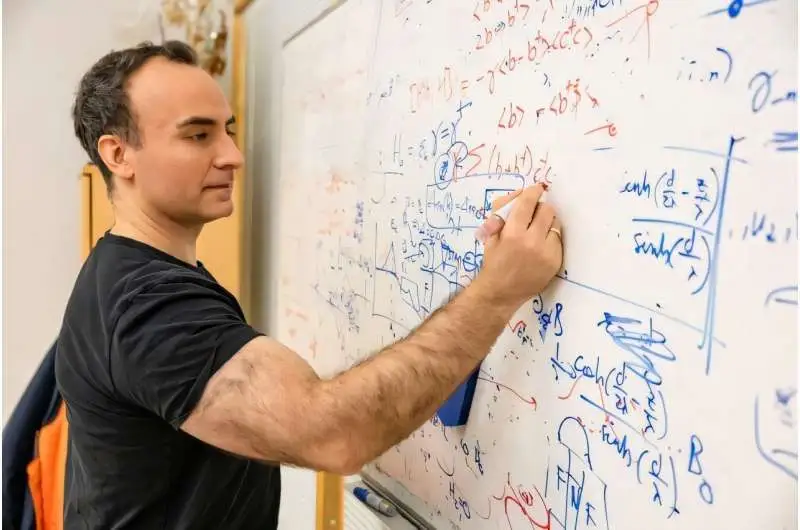
NbRe: First Triplet Superconductor at 7 K
Physicists found triplet Cooper pairs in niobium-rhenium at 7 K — opening a path to fault-tolerant topological quantum computers.
Spider Silk 5x Tougher Than Steel: Molecular Secret Cracked
Scientists decoded the exact molecular switch — arginine-tyrosine bonds — that turns liquid protein into spider silk, a thread 5x tougher than steel.
NVIDIA Cosmos 2026: Open AI That Teaches Robots Physics
Open-source platform from NVIDIA generates physics-accurate worlds so robots learn without real crashes. Free models, 12M training hours.