Google: Quantum Encryption Cracking by 2029
Authors: Heather Adkins, Sophie Schmieg
On March 25, 2026, Google VP of Security Engineering Heather Adkins and senior cryptography engineer Sophie Schmieg published a blog post titled «Quantum frontiers may be closer than they appear.» Inside was a concrete deadline: by 2029, Google plans to complete its migration to encryption that resists quantum attacks. The company recommends others do the same.
What Breaks and Why
The modern internet rests on two mathematical problems: factoring large numbers (RSA) and the discrete logarithm on elliptic curves (ECC). Classical computers need millennia. A quantum computer with enough qubits solves both in hours — using Shor’s algorithm, known since 1994.
Shor’s algorithm — a quantum algorithm that finds the period of functions exponentially faster than any classical method. Period-finding is the step that lets you factor a number into primes and crack RSA.
At risk: HTTPS, TLS, VPN, SSH, digital signatures, PGP email encryption, blockchain wallets. Everything protected by RSA or ECC — which is essentially all encrypted traffic on the internet.
105 Qubits vs 4 Million
Google’s quantum chip Willow, unveiled in December 2024, packs 105 physical qubits. Breaking RSA-2048 requires 4 to 20 million — a gap of five orders of magnitude.
But Willow demonstrated something more important than qubit count: for the first time, increasing the error-correction code size made error rates drop rather than rise. That removes the central technical objection — that scaling is impossible.
«Harvest Now, Decrypt Later»
Google stresses that the threat is not in 2029. It is right now. Intelligence agencies and hackers have been intercepting encrypted traffic and storing it for over a decade. When a quantum computer arrives, they will decrypt the archive. Medical records, government communications, financial data — anything stored longer than a few years is already exposed.
SNDL (Store Now, Decrypt Later) — a strategy where an attacker intercepts encrypted data today, planning to decrypt it in the future with a quantum computer.
Defenses Already Exist
NIST finalized three post-quantum cryptography standards in August 2024: ML-KEM (lattice-based key encapsulation), ML-DSA (digital signatures), and SLH-DSA (hash-based backup). These algorithms resist Shor’s attack.
Google is already deploying them: Android 17 uses ML-DSA for signatures, Chrome supports post-quantum TLS. Apple added PQC to iMessage back in 2024. Signal did it in 2023. The bottleneck is not missing solutions — it is migration speed. Rebuilding global PKI infrastructure takes 5-10 years.
Skeptics and Realists
Leonie Mueck, former CTO of quantum startup Riverlane, told The Guardian: Google does not claim a working quantum computer will arrive by 2029. Most experts say the 2030s; some say the 2050s. Cooling to fractions of a kelvin, aligning lasers for weeks, infrastructure on the scale of a power plant — this is not a software problem with exponential growth curves.
But Google’s argument is not that Q-Day hits in 2029. The argument is that migration must start now, because SNDL attacks are already happening and infrastructure overhauls take years.
The post was published on blog.google on March 25, 2026 and represents the company’s official position, not a peer-reviewed study.
References
Related Articles
AI Designs 100 Quadrillion Proteins in a Single Run
JURA Bio's Variational Synthesis method cut protein synthesis costs a trillion-fold, producing 10^17 unique molecules in one reaction.
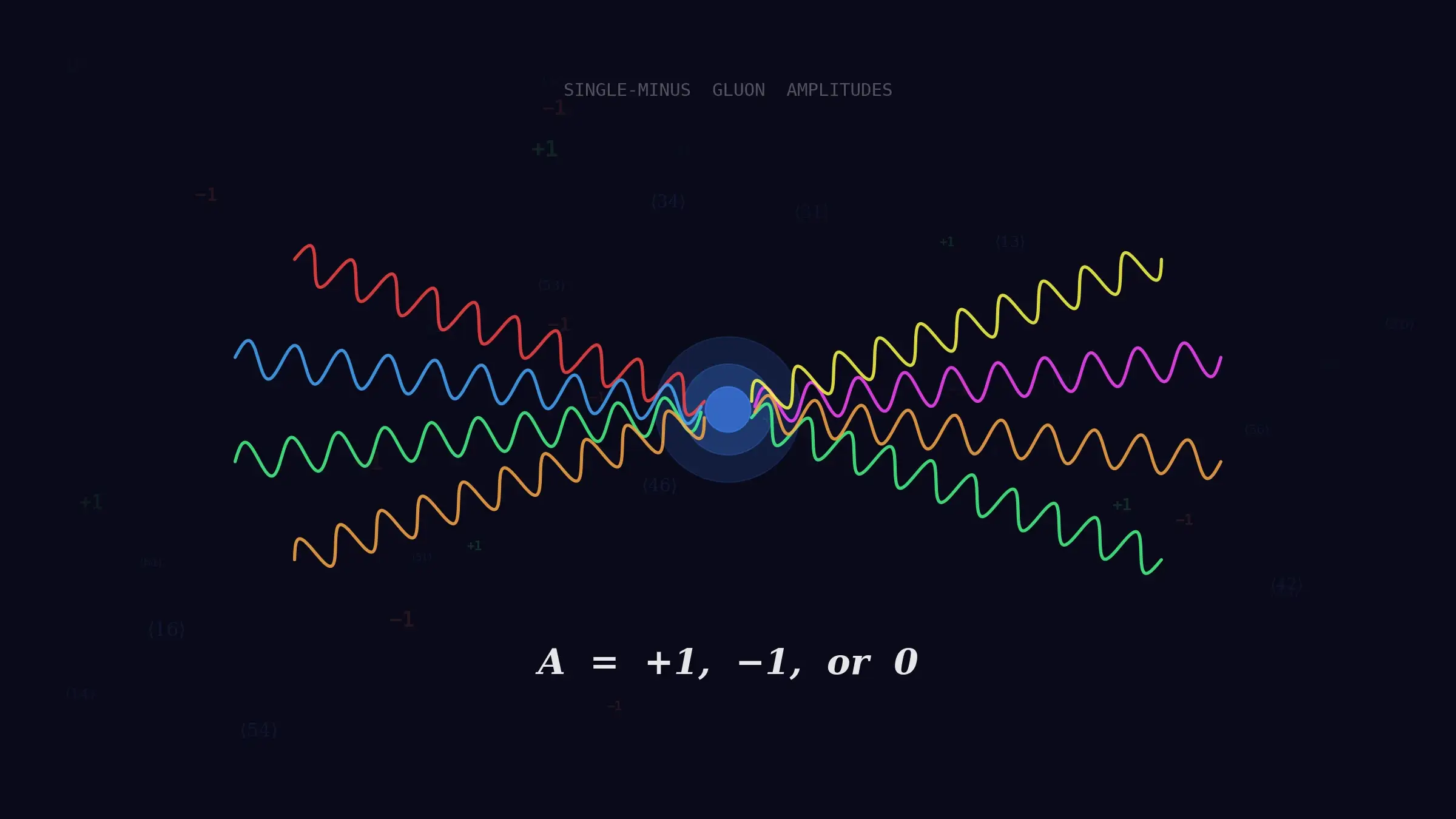
GPT-5.2 Cracked a 40-Year Gluon Mystery
OpenAI's model conjectured a formula for gluon amplitudes assumed zero since 1986. Physicists from Harvard and Cambridge confirmed it was right.
NVIDIA Cosmos 2026: Open AI That Teaches Robots Physics
Open-source platform from NVIDIA generates physics-accurate worlds so robots learn without real crashes. Free models, 12M training hours.